Have you ever imagined a world where your devices communicate with each other seamlessly, making your life more convenient and efficient? This vision is becoming a reality through the Internet of Things (IoT), a transformative technology that is reshaping industries and revolutionizing the way we interact with the world around us. But what exactly is the Internet of Things, and how does it work? Let’s delve into this fascinating realm of interconnected devices and explore its implications for the future.
What Is the Internet of Things?
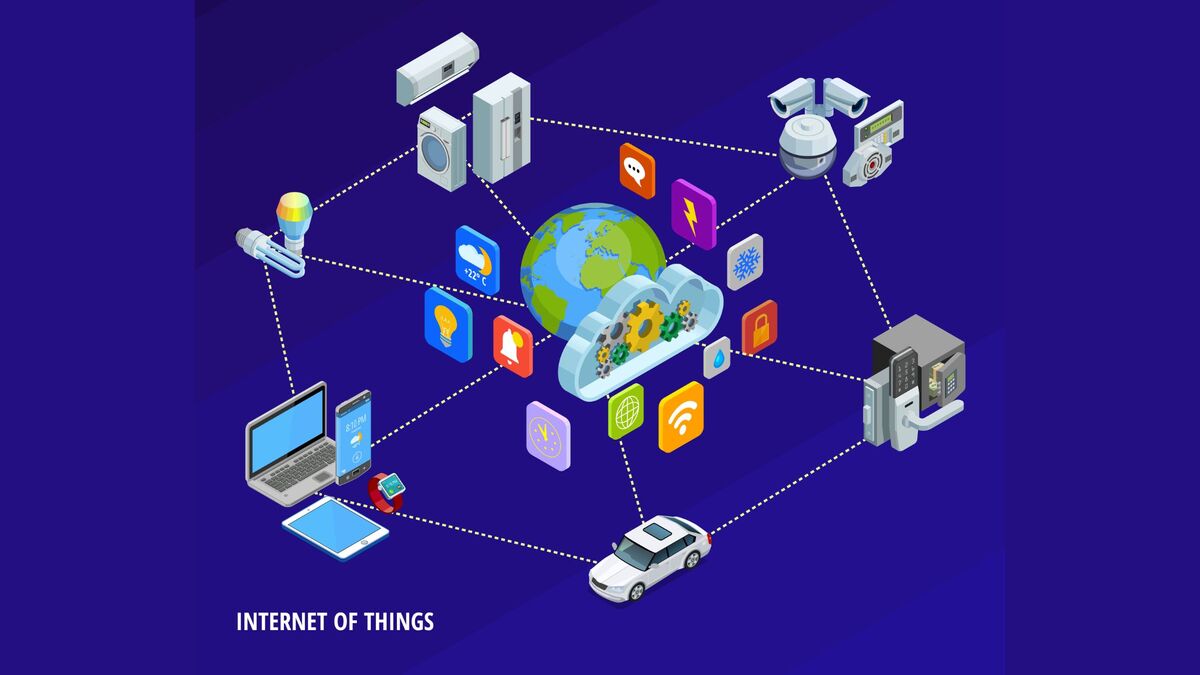
The Internet of Things (IoT) refers to a vast network of interconnected devices, sensors, and objects that collect and exchange data over the internet. These devices are equipped with embedded sensors, software, and connectivity capabilities, enabling them to communicate with each other and perform various tasks autonomously. From smart thermostats and wearable fitness trackers to industrial machinery and autonomous vehicles, IoT technology is transforming virtually every aspect of our lives and industries.
How Does IoT Work?
At the core of IoT technology is the ability of devices to collect, transmit, and analyze data in real-time. This process typically involves four main components:
- Sensors and Devices: IoT devices are equipped with sensors that gather data from their surroundings, such as temperature, humidity, motion, and location. These sensors can range from simple environmental sensors to sophisticated cameras and industrial machinery.
- Connectivity: Once data is collected, IoT devices use various communication protocols, such as Wi-Fi, Bluetooth, Zigbee, or cellular networks, to transmit the data to centralized servers or other connected devices.
- Data Processing and Analytics: The data collected by IoT devices is then processed and analyzed using cloud-based platforms or edge computing systems. Advanced analytics algorithms are applied to derive insights, detect patterns, and make intelligent decisions in real-time.
- Action and Response: Based on the insights derived from data analysis, IoT devices can initiate actions autonomously or send commands to other connected devices to trigger specific responses. For example, a smart thermostat can adjust the temperature based on occupancy patterns, or a connected car can reroute its navigation based on traffic conditions.
Challenges and Considerations:
While the Internet of Things offers tremendous potential for innovation and efficiency, it also presents several challenges and considerations, including:
- Security and Privacy: With the proliferation of connected devices, ensuring the security and privacy of data becomes paramount. Vulnerabilities in IoT devices can pose significant risks, including data breaches, unauthorized access, and cyber-attacks.
- Interoperability: The diverse ecosystem of IoT devices and platforms can lead to interoperability challenges, making it difficult for devices from different manufacturers to communicate seamlessly.
- Scalability and Infrastructure: As the number of connected devices continues to grow exponentially, scalability and infrastructure become critical considerations. Ensuring robust network connectivity, bandwidth, and data storage capabilities is essential to support the expanding IoT ecosystem.
Are We Ready to Embrace the Connected Future of IoT?
In conclusion, the Internet of Things represents a paradigm shift in how we interact with technology and the world around us. By connecting billions of devices and harnessing the power of data, IoT technology is driving innovation, efficiency, and new opportunities across industries. However, realizing the full potential of IoT requires addressing various challenges, including security, interoperability, and scalability. As we continue to explore the possibilities of the Internet of Things, one thing is clear: the future is undoubtedly connected. What steps can businesses take to mitigate security risks associated with IoT devices in their networks?
FAQs:
The Internet of Things (IoT) refers to a network of interconnected devices, sensors, and objects that collect and exchange data over the internet.
IoT devices are equipped with sensors to gather data, which is then transmitted over the internet using various communication protocols. This data is processed and analyzed to derive insights, enabling devices to perform tasks autonomously or trigger responses in other connected devices.
Examples of IoT devices include smart thermostats, wearable fitness trackers, home security cameras, connected cars, industrial machinery, and smart appliances like refrigerators and washing machines.
IoT technology offers numerous benefits, including improved efficiency, enhanced convenience, real-time monitoring and control, predictive maintenance, and data-driven insights for better decision-making.
Challenges associated with IoT include security and privacy concerns, interoperability issues between devices and platforms, scalability and infrastructure requirements, and potential for data overload.
IoT is revolutionizing industries such as healthcare, manufacturing, transportation, agriculture, and smart cities. It is enabling innovations like remote patient monitoring, predictive maintenance in manufacturing, autonomous vehicles, precision agriculture, and efficient urban infrastructure management.
To ensure security in IoT devices, measures such as implementing strong encryption protocols, regularly updating device firmware and software, using secure authentication methods, and deploying intrusion detection systems can be employed. Additionally, educating users about security best practices is crucial.
Data privacy in IoT is managed through practices such as data encryption, anonymization of personally identifiable information, obtaining user consent for data collection and usage, and compliance with data protection regulations such as GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act).









I was examining some of your posts on this site and I think this website is really instructive! Continue posting.